Bothin, A., and Clough, P. Participants’ personal note-taking in meetings and its value for automatic meeting summarisation. Information Technology and Management (December 2011), 1–19. [PDF]
—–
This paper reports the results of a quantitative study on how people take notes in meetings. The goal of the authors was that of aiding the design of innovative applications to support work-related meetings.
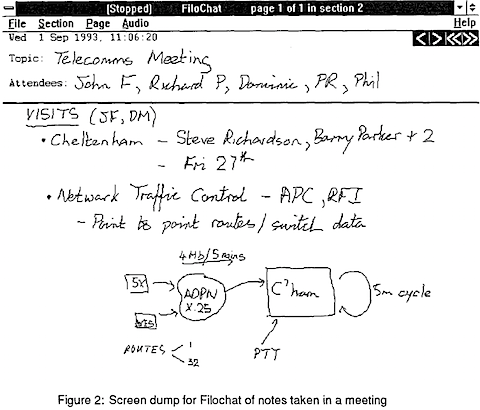
Notes taken during meetings have a pivotal role in helping people understand what happened during the meeting and to recall important information or decisions that were shared during the gathering. Taking notes is usually a tedious activity and therefore lots of scholar have focused on work-related meetings, trying to come up with automatic solutions to summarize what happened during the interactions.
The paper reports interesting references to studies that demonstrate a relation between acoustic features (i.e., pitch, intensity, speaking speed, and pauses) of the recordings of the meetings and annotations created by participants (Arons, 1994; Kennedy & Ellis, 2003).
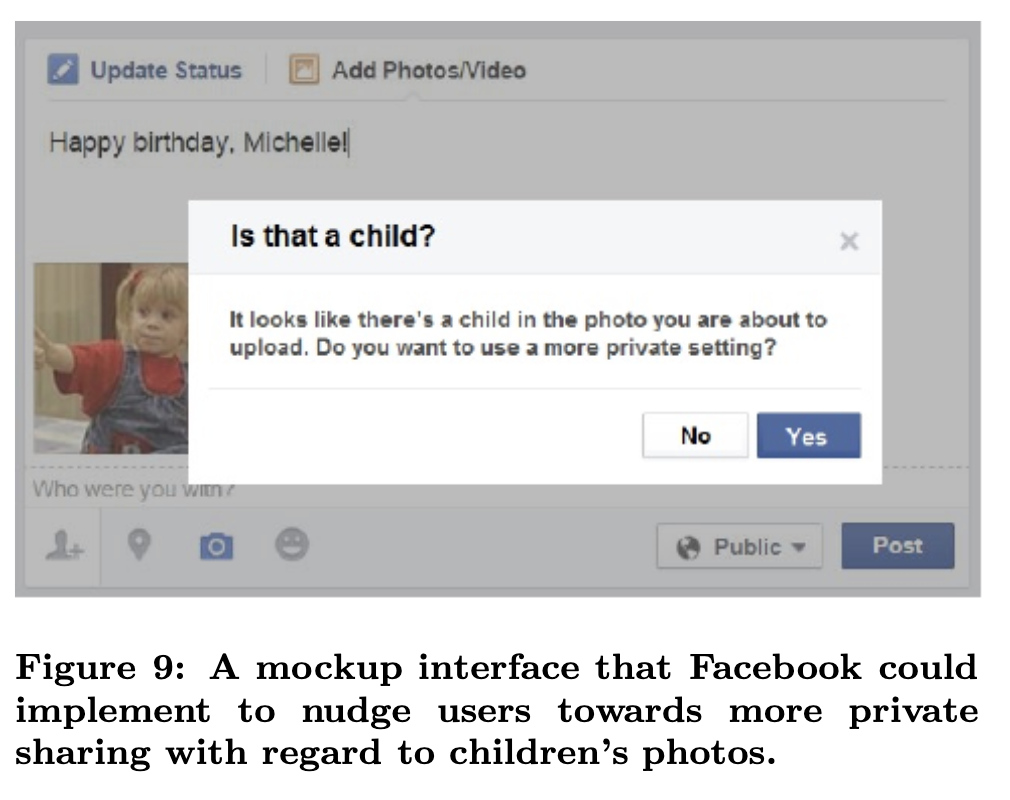
Also, some possible implications in the design of systems to support annotations: shared note-taking was investigated by Landay & Davis, 1999 and by Wolf et al., 1992. Finally, the possibility to suggest notes to participant was examined by Banarjee & Rudnicky, 2009.
The paper describes interesting related work on how people take notes for personal reasons. These notes are created in daily life meetings regardless of whether specific instructions to create summaries are given to participants. Note-taking mainly takes place tin order to create a personal record to aid remembering what was being discussed. Participants in meetings usually take notes of the most informative events. They contain “personally important” points and details on action items assigned to the note-taker. Most relevant references for these findings are the studies of Khan, 1992; Whittaker et al., 2005; and Wittaker et al., 2008.
These studies point out that during work meetings only salient and personally interesting points are recorded. The notes people generally take are short (i.s., 20-30 s long on average) [Khan, 1992]. These notes are likely to have predictive power for finding the most important parts of meetings.
The same authors examined the role of of individual differences in talking and note-taking activities in meetings (Bothin & Clough, 2010). Participants had different behaviour according to their gender, age, and native language. Women wrote more but men talked more within meetings. The older the participants were, the more they talked and noted. Native English speakers wrote more, but there was no significant difference in talking behavior.
In their experiment, Bothin & Clough examined the AMI corpus, involving 104 participants in total, and found that personal notes were generally short. Single items were around 8 seconds long on average (SD 3). They found a positive correlation between the total meeting length and the total number of the notes (r = 0.21), as well as the total meeting length and the total duration of the notes (r = 0.20). Perhaps people prefer to write down key words only [Khan, 1992] and every time something important to them occurs in the discussion.